Ransomware Trends Shaping Cybersecurity in 2026
New research from the 2026 Cyber Threat Outlook reveals how ransomware operations are evolving alongside identity attacks, AI-powered cybercrime, and vulnerable edge infrastructure.
- Ransomware groups continue exploiting VPN and edge vulnerabilities
- Credential theft and identity compromise often enable ransomware intrusions
- Double-extortion tactics remain a primary pressure tactic
- Attackers increasingly automate reconnaissance and lateral movement
Understand how ransomware tactics and other cyber threats are evolving and what security teams should prepare for next.
Ransomware and Cyber Threat Trends in this Report
Ransomware isn’t slowing down
Edge flaws are the weakest link
High-value systems targeted
Faster attacks, lower barriers
Who this report helps
Security and IT leaders responsible for protecting organizations from ransomware and evolving cyber threats, including:
-
CISOs and security leaders: Understand how identity attacks, AI-driven threats, and edge vulnerabilities are evolving.
-
IT and infrastructure teams: Learn how attackers exploit VPNs, collaboration tools, and cloud identities.
-
Security analysts: Gain insight into real intrusion patterns and emerging attacker techniques.
Built on real threat intelligence
This report draws on frontline investigations, security telemetry, and incident response insights from Field Effect’s global security teams, including:
-
Security telemetry from production environments
-
Real incident investigations
-
Threat intelligence analysis
-
Global security expert contributions
GET YOUR FREE REPORT
Download the 2026 Cyber Threat Outlook
Ransomware continues to evolve alongside identity attacks, AI-driven reconnaissance, and vulnerable edge infrastructure.
This research analyzes the attack patterns and techniques security teams must prepare for next.
- How ransomware operators gain initial access
- Why identity compromise often precedes ransomware attacks
- The infrastructure vulnerabilities attackers exploit most
- How ransomware ecosystems continue to expand
Get clear analysis and actionable insights from the cybersecurity experts at Field Effect.
Cybersecurity for every size business.
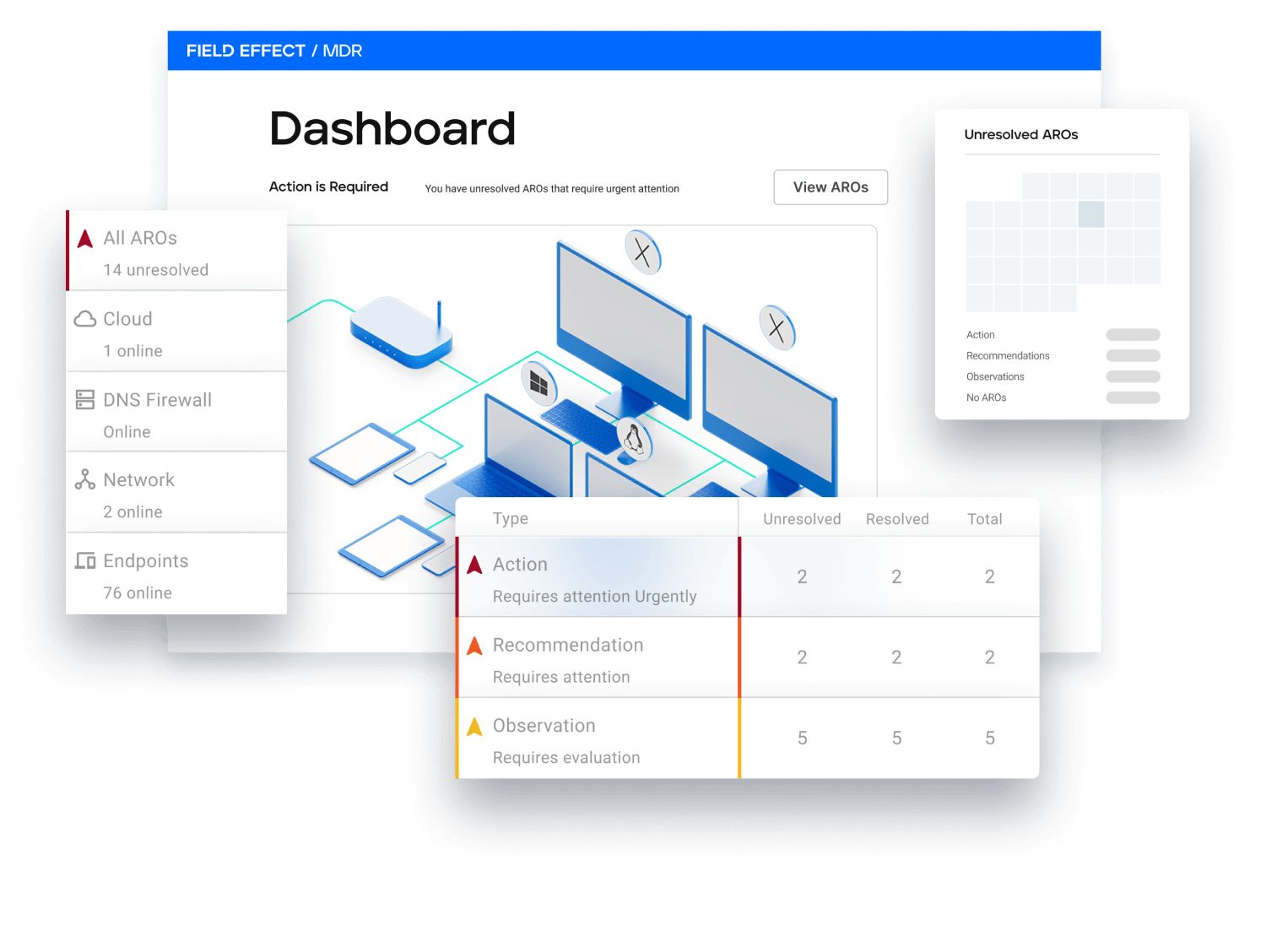
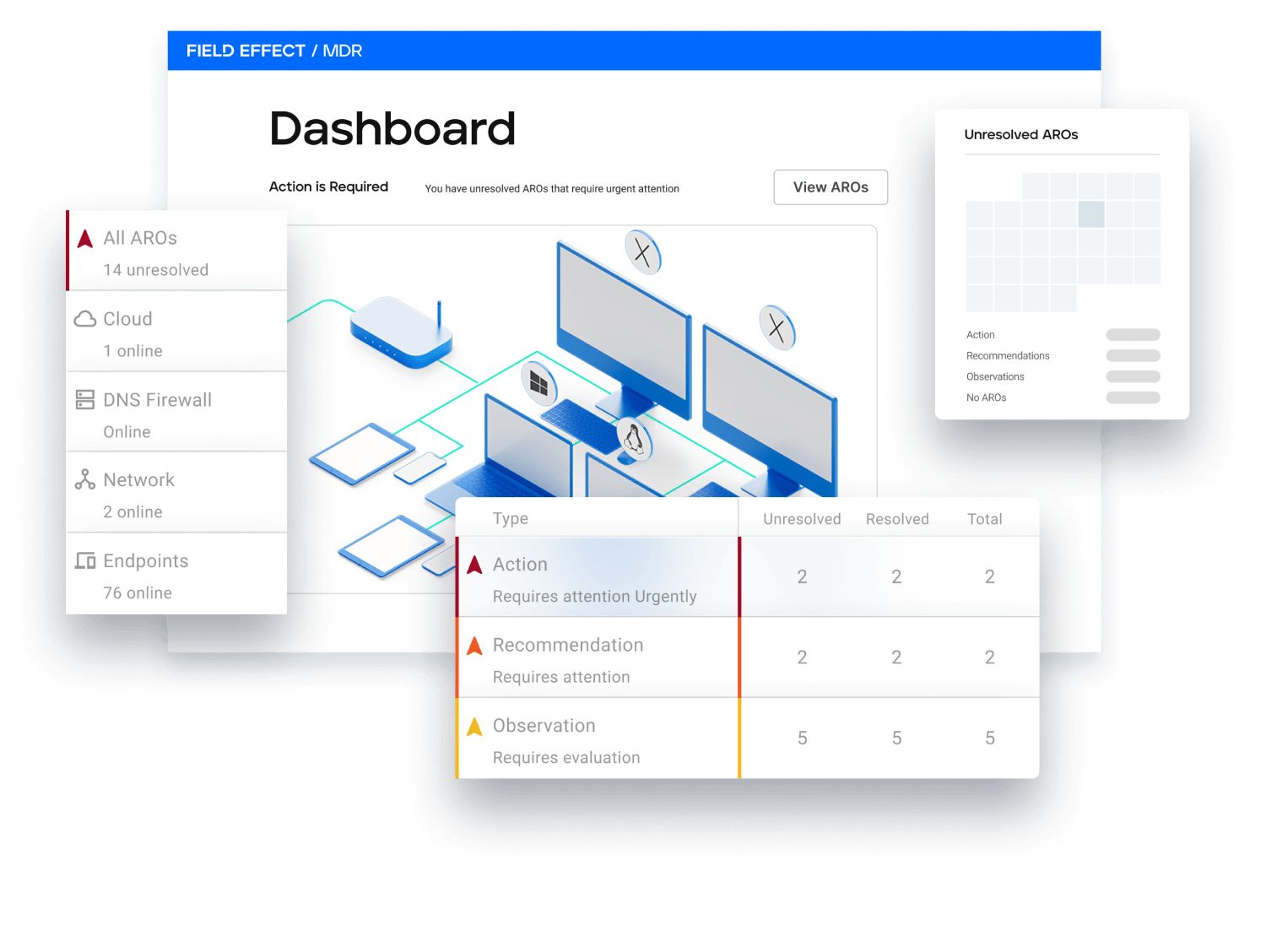
Field Effect MDR™ rapidly prevents, detects, and responds to threats all from one platform, minimizing complexity for you and maximizing defense for your clients.

Trusted above the rest
Users rank Field Effect MDR the leading solution.
See what our users have to say




The standout feature is its continuous 24/7 monitoring of all network traffic, providing unparalleled vigilance.
It has taken the place of several cybersecurity solutions for us, including replacing a previous SOC vendor.
We now have a single cybersecurity product that protects all of our threat surfaces, and all the endpoints.
I'd recommend the product. I'd rate the solution ten out of ten.
But in the event that someone clicks on something they shouldn't, [Field Effect MDR] will isolate it and quarantine it.
CyberSecurity is our Priority
About Field Effect
Field Effect, a global cybersecurity company, is revolutionizing the industry by bringing advanced cybersecurity solutions and services to businesses of all sizes. We build solutions that are sophisticated, yet easy to use and manage, so every business owner can get the hands-free cybersecurity they expect and the sleep-filled nights they deserve.
